That Call From Google Support? It's a Scam — How Vishing Attacks Target Small Businesses
Scammers are spoofing Google's real phone number to steal business accounts. Here's how vishing attacks work and what your team needs to know.
RNITS Blog
Scammers are spoofing Google's real phone number to steal business accounts. Here's how vishing attacks work and what your team needs to know.

An AI model just found thousands of zero-day vulnerabilities in every major OS and browser. Here's what small businesses need to know — and do — right now.

Attackers don't always hack systems — they hack people. This guide explains how social engineering targets help desks and what small businesses can do to stop it.
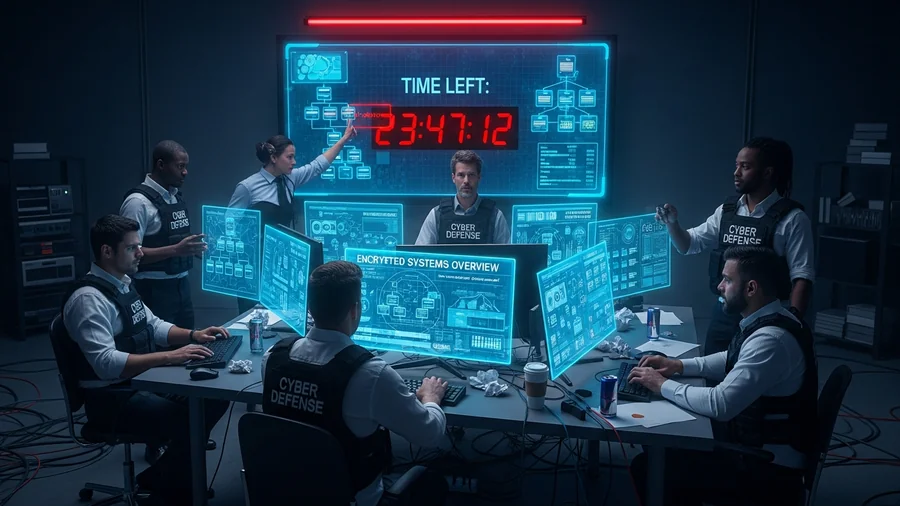
The first 24 hours after a ransomware attack shape the cost, downtime, and recovery path. This guide explains how ransomware recovery services work and how businesses should build a response plan before an incident happens.

Having computer support for business is no longer optional – it’s essential. Every company, big or small, relies on technology to operate efficiently, communica

Ransomware backup protection is one of the most critical defences in modern cybersecurity. As cybercriminals continue to use advanced tactics to lock, encrypt,