· RNITS · Cybersecurity Service · 11 min read
The Un-MSP Approach: Why SMBs Overpay for Security Tools They Don't Need
Most SMBs are paying for 10 security tools that overlap on the same controls and still miss real gaps. Here's why — and how to stop.

It still blows our minds how much small businesses overpay for security.
A 12-person law firm in southern New Hampshire called us last year. They were paying their MSP a monthly bill that would make a mid-size enterprise wince. When we laid out everything they were being charged for, we counted nine separate security products on the invoice. Three of them did essentially the same job. Two of them covered controls the firm did not actually need. And there were still real gaps — things an auditor would flag — that none of the nine tools touched.
After we rebuilt their stack around what they actually needed, their monthly bill dropped by roughly half. Same level of protection. Better coverage in the places that mattered. Fewer tools to manage. Fewer logins for their people to remember.
This is not a one-off. It happens constantly. And the reason it happens is not because MSPs are evil — it is because the industry runs on a simple formula: more tools on the invoice means a bigger invoice. Nobody audits the stack against the actual risk. The SMB trusts their MSP. The MSP keeps stacking. Years go by. The bill creeps up. Nobody asks hard questions.
We think that model is broken. That is why we call ourselves the un-MSP.
The MSP oversell problem
Walk into any traditional MSP’s sales pitch and you will hear a similar script. Layered security. Defense in depth. Endpoint protection plus EDR plus MDR plus XDR. Email security plus a second email security tool for redundancy. DNS filtering plus web filtering plus browser isolation. Backup software plus a separate cloud backup plus immutable storage plus a disaster recovery tool. SIEM plus a log aggregation platform. Plus a compliance tool. Plus a phishing simulation platform. Plus a password manager. Plus a ticketing system that the SMB is paying for but never sees.
Every one of those products sounds important. Some of them really are. But most SMBs under 50 employees do not need all of them, and almost none of them need to be buying overlapping versions of the same control.
The problem is that traditional MSPs make money on the stack. A typical vendor arrangement looks like this: the MSP pays wholesale for a security product, marks it up 50 to 200 percent, and bills it to the client as a per-seat line item. Multiply that by eight or ten products across fifty seats and the margin is substantial. There is zero incentive for the MSP to remove a tool. There is strong incentive to keep adding them.
This is not a secret in the industry. It is just not something MSPs talk about with clients.
Why SMBs do not push back
Small business owners are not security experts. They did not start their company to become one. They hired an MSP specifically so they would not have to understand every acronym and every line item on the invoice.
So when the invoice shows up with a list of products they do not fully understand, they pay it. The MSP has told them these things are necessary. The alternative — challenging the recommendation — feels like questioning the dentist about the filling. Most people do not do that.
A few patterns make this worse:
- The bundle effect. Many MSPs bill everything as one monthly per-user fee. The SMB sees a single number. They never see the underlying line items or the markup on each one.
- Compliance panic. HIPAA, PCI, SOC 2, cyber insurance questionnaires — all of these create pressure to buy more tools so the SMB can check a box. MSPs use this pressure to justify additional products, whether or not those products actually improve security.
- Fear-based selling. Ransomware headlines make it easy to sell any new security product as “necessary.” Most SMBs are not in a position to evaluate whether the threat model justifies the cost.
- Switching cost. After a year or two with an MSP, the SMB assumes that changing providers will be painful. So they stay — and they keep paying.
None of this is the SMB’s fault. They are doing exactly what the industry trained them to do. The fault is with an industry that profits from opacity.
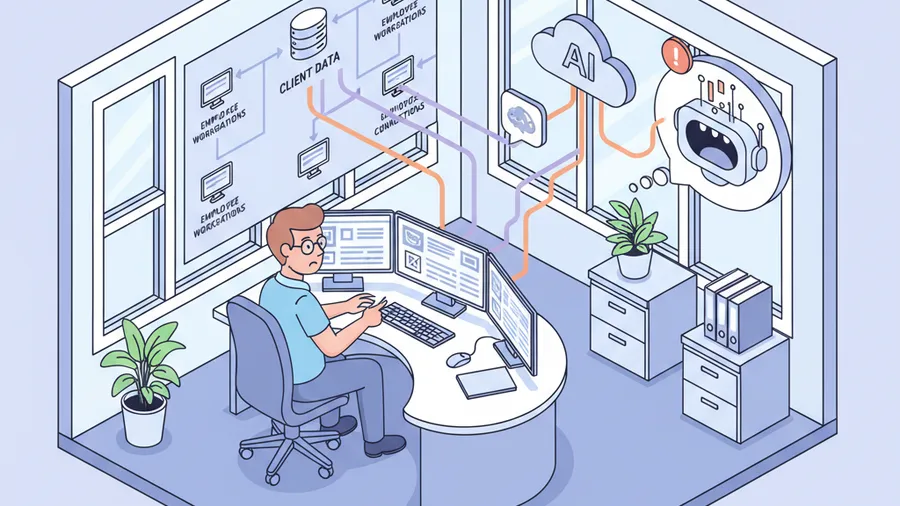
What tool sprawl actually looks like
Here is a sanitized version of what we saw at the law firm. The names have been changed — the shape of the problem has not.
They had three products that all claimed to do endpoint protection. One was a traditional antivirus. One was an EDR platform. One was an MDR service that also included endpoint telemetry. All three agents were running on every workstation. Two of them were flagging the same events. The third was a different vendor’s version of the second. They were paying per seat for each one.
They had two email security products. One was built into their Microsoft 365 tenant and was already included in the license they were paying for. The other was a third-party add-on that duplicated most of what the Microsoft tooling did.
They had a compliance tool that generated reports nobody at the firm ever opened.
They had a phishing simulation platform that nobody ran campaigns on.
They were paying for a dark web monitoring service that sent alerts to an inbox the managing partner never checked.
And here is the kicker — with all nine products running, they still had real gaps. Their conditional access policies in Microsoft 365 were wide open. MFA was inconsistently enforced. Their admin accounts were not separated from daily-use accounts. There was no documented incident response plan. Backup restoration had not been tested in eighteen months. An actual attacker would have walked past most of the layered tooling and hit the gaps.
This is tool sprawl. It is not just expensive — it is actively misleading. It creates the feeling of security without the substance. You look at the stack and think “we are protected.” But protection comes from coverage of the right controls, not from the number of logos on your invoice.
The right way to think about security spend
Security is not a list of products. It is a list of controls.
A control is a specific thing you are trying to achieve — identity protection, endpoint visibility, email hygiene, data recovery, patch discipline, access governance, logging and monitoring, user awareness, incident response readiness. There are frameworks that spell these out in detail. CIS Controls is a common one. NIST has another. Cyber insurance carriers have their own. They all converge on the same basic set of things a business needs to be doing.
Every control can be covered by one product. Some products cover multiple controls. Most businesses under 100 employees can get full coverage of the controls that actually matter to them with four to six well-configured tools — not ten or twelve.
The question is not “how many security products do we have?” The question is “which controls are we covering, with what, and how well?” If you have three products all covering the same control and nothing covering the control next to it, you have spent more and gotten less. If your MSP cannot map their recommended stack to specific controls when you ask them to, that is a red flag.
This is the exercise most SMBs have never done. And it is the first thing we do when a new client comes to us.
Questions to ask your current MSP
If you already have an MSP and you are reading this and wondering whether you are being oversold, here are the questions that will tell you quickly:
- Can you show me every security product on my invoice and what control each one covers? A good MSP will have this ready. A bad one will get defensive or give you a vague answer about “defense in depth.”
- Where are my current gaps? If the answer is “you don’t have any,” something is wrong. Every environment has gaps. A good MSP will tell you what yours are and what the plan is to close them.
- What would you remove if I asked you to cut my bill by 20 percent? This is the killer question. A good MSP can answer it honestly. A bad one will tell you nothing is cuttable and everything is critical.
- When was my last restore test? If they cannot tell you, your backup strategy is theoretical.
- What is my incident response plan and who executes it? If there is no plan, all the detection tooling in the world is worth less than it should be.
- How much of my bill is markup on third-party licenses? Most MSPs will not want to answer this. You are entitled to ask.
You do not need to be a security expert to ask these questions. You just need to be willing to push back on the first vague answer you get.
What the un-MSP approach looks like
We built RNITS around a different assumption: that most small businesses are overpaying for security, that the overpayment comes from tool sprawl rather than overpriced tools, and that right-sizing the stack is almost always the fastest path to both better protection and lower cost.
In practice, that means a few things.
We audit before we sell. When a new client comes in, we do not walk in with a preloaded stack of products to bill them for. We look at what they already have, what their risks actually are, what their compliance obligations are, and what controls are currently uncovered. Then we build a recommendation from that — not from a vendor margin sheet.
We tell you what you do not need. This sounds obvious but it is the opposite of how most MSPs operate. If you are already paying for a tool that we would have recommended, we tell you to keep it and we do not rebill you for a substitute. If you are paying for something that overlaps with another tool on your invoice, we will flag it and help you drop the duplicate.
We favor consolidation over layering. Most environments under 100 employees can be secured well with a focused stack — identity, endpoint, email, backup, patching, monitoring, awareness — using tools that are already included in software you are probably paying for, plus a small number of purpose-built products to fill the gaps. We do not believe in stacking three products to cover one control.
We charge transparently. Our pricing is published. There is no obscure per-user math with hidden markups. You see what you pay and what you get.
We include the things most MSPs charge extra for. Security monitoring and management, patch management, remote monitoring, compliance alignment for frameworks like HIPAA, and incident response support are part of what we do, not separate line items designed to pad the invoice.
The result, for most clients, is that we deliver the same level of real-world protection their previous MSP was supposedly providing — often better — at a fraction of the cost. The law firm we mentioned earlier is one example. There are others. The pattern repeats because the problem is structural.
This is not anti-MSP — it is anti-oversell
To be fair, not every MSP is bloating invoices deliberately. Some of them genuinely believe more tools equals more security. Some of them are following a playbook they were taught by vendors and never questioned. Some are good operators working inside a bad pricing model that rewards volume over fit.
We are not against the MSP model. We are an MSP. What we are against is the version of it that treats small businesses as a margin opportunity instead of a partner to protect. The industry default should be “buy less, cover more.” Most of the time, it is the opposite. That is what we are trying to change.
If you are a small business owner in New Hampshire, Massachusetts, or anywhere we can reach, and you look at your monthly IT and security bill and quietly wonder whether you are paying for things you do not need — you probably are. That feeling is almost always right. It is worth investigating.
The best starting point is a second opinion from someone who is not trying to sell you another product.
See what you are actually paying for
We offer a free cybersecurity audit for small businesses that want an honest second look at their current security setup. No sales pressure. No preloaded stack. Just a clear breakdown of what your existing tools are doing, where the real gaps are, and what a right-sized setup would look like for a business your size.
If the audit shows that your current MSP has you dialed in and priced fairly, we will tell you that. If it shows you are overpaying by a large margin — which is what we usually see — we will show you the math, and you can decide what to do next.
The un-MSP approach starts with a conversation, not a quote.
Book your free cybersecurity audit or get in touch with our team. We will take it from there.